The Vercel Breach Hit Crypto Teams Hardest. Why Secure Signing Matters.
Back to articles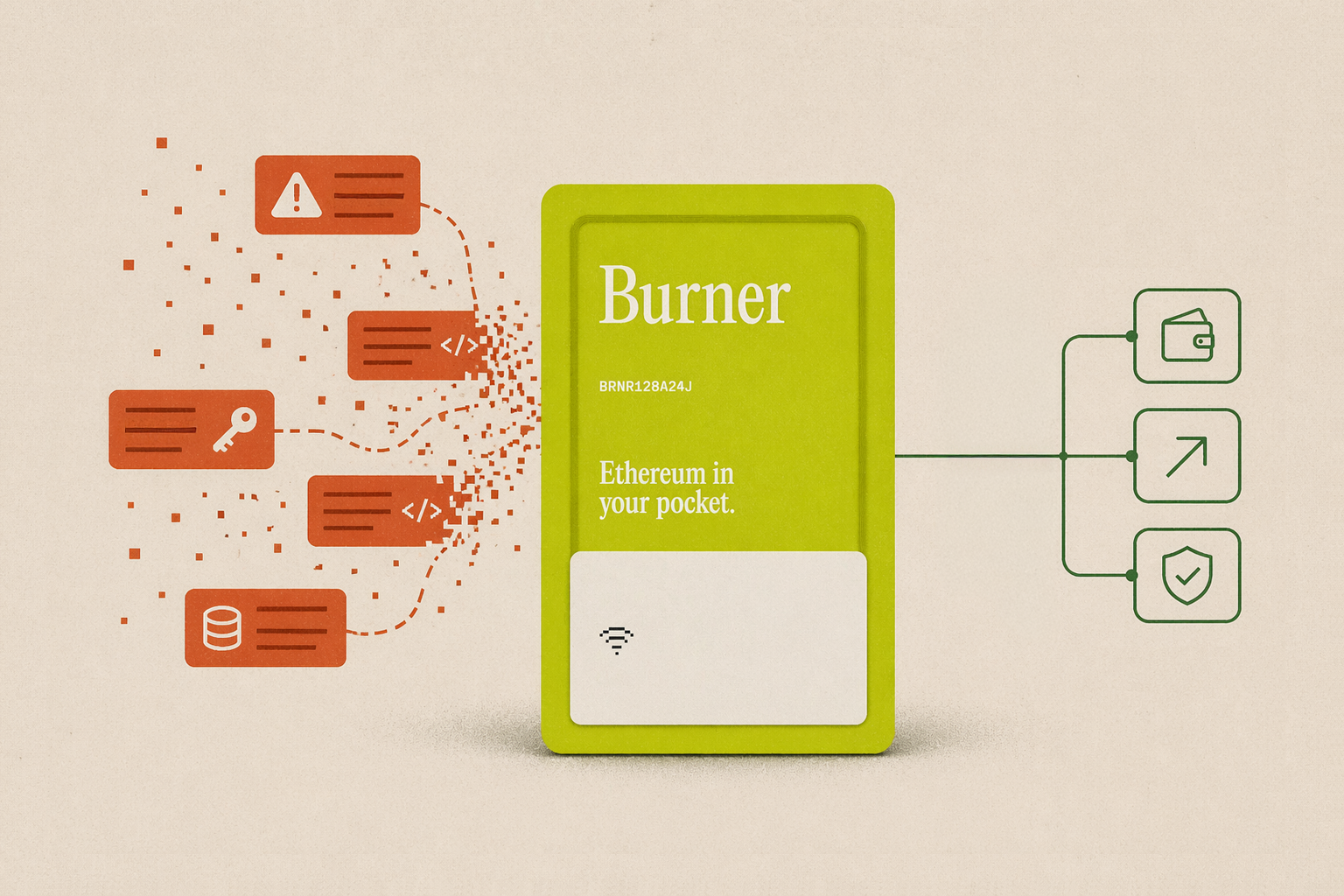
TL;DR
- Vercel confirmed a security breach on April 19, 2026. Attackers accessed API keys, database credentials, and deployment tokens for hundreds of customers.
- The attack started with malware on a Context AI employee's machine in February. From there, the attacker worked through a chain of stolen credentials into a Vercel employee's account and then into Vercel's internal systems.
- Crypto teams are most exposed because leaked credentials can lead to irreversible financial loss. Many Web3 projects store keys that connect to wallets, payment processors, and blockchain infrastructure in Vercel's environment variables.
- Vercel classifies environment variables as either "sensitive" (encrypted, unreadable after saving) or "non-sensitive" (stored as readable plaintext). Only the non-sensitive variables were exposed, but many teams stored critical secrets there without realizing the difference.
- The fix goes beyond rotating keys. Your most important signing keys should live on hardware you control, not on a platform that can be breached. A hardware wallet like Burner stores private keys on a secure chip where they can never be extracted or copied.
On April 19, 2026, Vercel posted a security bulletin confirming that someone had been inside their systems, accessing customer environment variables that weren't encrypted at rest.
Environment variables are where most crypto teams store the keys that connect frontends to backend infrastructure: RPC nodes, wallet services, payment APIs, database credentials. Vercel lets you mark environment variables as either "sensitive" (encrypted, unreadable after saving) or "non-sensitive" (decryptable to plaintext). The breach didn't touch the sensitive ones. But the non-sensitive variables were exposed for what Vercel called a "limited subset" of customers. That subset turned out to include "hundreds of users across many organizations."
For most SaaS companies, a credential rotation is annoying. For crypto teams, a compromised API key can lead directly to stolen funds.
How the Breach Actually Happened
In February 2026, an employee at Context AI got hit with Lumma Stealer malware. The infection likely came from downloading game exploits. It harvested their Google Workspace credentials along with keys for Supabase, Datadog, and Authkit.
One of those stolen accounts had a connection to Vercel. A Vercel employee had signed up for Context AI's Office Suite using their corporate Google account, giving it broad access. The attacker used that connection to get into the Vercel employee's Google Workspace, and from there into Vercel's internal environments and customer data.
Context AI Employee
The stolen data reportedly appeared on a cybercrime forum with a $2 million asking price. According to Vercel's postmortem, they brought in Mandiant, Google's cybersecurity incident response team. Mandiant confirmed that Next.js, Turbopack, and their npm packages weren't compromised, but customer environment variables were exposed.
Why Crypto Teams Are Most Exposed
When a SaaS company loses an API key, the damage is usually operational: broken integrations, maybe some downtime. When a crypto team loses a key, the damage can be financial and permanent.
CoinDesk reported that the breach "sent crypto developers scrambling to lock down API keys." Solana-based exchange Orca was named as one of many Web3 teams that host wallet interfaces and dashboards on Vercel.
Crypto teams have been known to store credentials like these in Vercel environment variables:
RPC endpoint keys: Alchemy, Infura, QuickNode, and similar providers. These let attackers monitor transactions, front-run trades, or map your wallet infrastructure.
Wallet service credentials: Fireblocks, Turnkey, Privy, among others. Depending on the integration, these can grant transaction-signing access.
Payment processor API keys: Stripe, Circle, MoonPay. These connect to real money movement.
Smart contract deployer private keys: some teams store contract deployment keys as env vars. If those same keys hold admin privileges on live contracts, the exposure is catastrophic.
Database credentials: Supabase, PlanetScale, MongoDB Atlas, and others. User data, transaction histories, internal records.
If any of these were marked "sensitive" in Vercel, they stayed encrypted. If they were stored as non-sensitive variables, which decrypt to plaintext internally, they may have been exposed.
Small crypto teams tend to reuse keys across environments. The same API key might run both staging and production. Sometimes the signing key that deploys contracts is the same one with admin access to the live protocol. When one of those keys leaks, the attacker doesn't need to compromise your smart contracts directly.
Even larger teams with separate staging and production environments still store secrets on someone else's infrastructure. If the platform gets breached, any key stored there is potentially exposed.
What to Do Right Now
Why Critical Transactions Need a Hardware Signer
When a platform gets breached, every secret stored there is compromised at once. Rotating keys and tightening classifications fixes the immediate exposure, not the underlying problem.
API keys and database credentials can be rotated. Signing keys are harder. If a compromised credential can approve a treasury transfer or upgrade a contract, rotating it after the fact doesn't undo the damage.
Routine operations like gas payments and small automated transactions will probably always run on hosted infrastructure. But critical transactions should require a second signature from a device that no platform breach can reach.
Burner wallet does this. It's a credit-card-sized hardware wallet that generates its own private key on a secure chip. That key never leaves the device. There's no seed phrase, no mnemonic, nothing that could end up in an env var or a password manager. The key exists in one place: on the card. If you need a backup, Burner cards can be duplicated directly to a second card without exporting the key as text. Your backup stays hardware-bound, not digital.

And with a protocol like Safe, you can set up a multisig wallet where Burner is one of the required signers. Your everyday operational wallet stays on a laptop or in a browser extension. The Burner card stays somewhere separate: a locked drawer, a safe, with a second team member. When a transfer, contract upgrade, or authorization needs approval, someone taps the card, enters the PIN, and co-signs. The transaction can't execute without it.
Traditional hardware wallets like Ledger and Trezor can also work as co-signers, but they introduce a risk. During setup, those devices generate a 12- or 24-word recovery phrase. In practice, teams often store that phrase in a password manager, a shared vault, or a document on someone's laptop. If any of those live on hosted infrastructure, a breach like Vercel's could expose the seed phrase the same way it exposed API keys.
Burner also works as a shared team wallet for small teams that use a single wallet for gas, bounties, or operational expenses. Keep the card in a secure location with a known PIN. When someone leaves, rotate the PIN. There's no seed phrase to re-secure.
Protecting keys from platform breaches is just one use case. From gifting crypto to inheritance planning, see 15 Real-Life Ways People Use Burner
Final Thoughts
The Vercel breach wasn't caused by Vercel writing bad code or ignoring security basics. It was caused by a series of trust failures across three organizations (Context AI, Google, and Vercel) that led to exposed customer credentials.
The same pattern exists for every team running crypto infrastructure on hosted platforms. Another breach like this will happen at a different provider, through a different vector. Rotate your keys, reclassify your environment variables, and require a hardware co-signer like Burner for any transaction that moves real money.
FAQ: Vercel Breach and Crypto Key Security
❓ Were crypto wallets directly hacked in the Vercel breach?
No. The breach exposed environment variables, not wallet private keys stored on-chain. But if a team stored wallet service API keys, signing credentials, or contract deployer keys as non-sensitive Vercel env vars, those specific keys are potentially compromised. The risk depends on what was stored and how it was classified.
❓ How do I know if my Vercel project was affected?
Vercel directly notified affected customers. But their scope has expanded since the initial disclosure. Check your environment variables: if any weren't marked "sensitive" and contain credentials that control funds or user data, rotate them regardless of whether you received a notification.
❓ What's the difference between "sensitive" and "non-sensitive" env vars in Vercel?
Sensitive environment variables are encrypted at rest and can't be read after they're set. You can only overwrite them. Non-sensitive variables can be decrypted to plaintext, which means anyone with access to Vercel's internal systems could read them. Mark everything important as "sensitive."
❓ Should crypto teams stop using Vercel?
Not necessarily. Vercel is fine for hosting frontends and serving static content. The lesson is about what you store there, not where you host. Keep read-only API keys on Vercel. Keep signing keys, admin keys, and treasury credentials on hardware you control.
❓ How does a hardware wallet protect against platform breaches?
A hardware wallet like Burner generates and stores its private key on-chip. The key never leaves the device and never exists on any server. Unlike traditional hardware wallets, Burner has no seed phrase that could end up stored digitally. When used as a co-signer in a multisig setup, critical transactions can't execute without physical authentication on the card.
❓ Why use Burner over a Ledger or Trezor to protect keys from platform breaches?
Ledger and Trezor generate a 12- or 24-word recovery phrase during setup. Teams often store that phrase in a password manager or shared vault, which puts it back on hosted infrastructure that a breach can reach. Burner generates its private key on a secure chip with no seed phrase at all. The key never leaves the card and never exists as text. If you need a backup, you duplicate the key directly to a second card. That means there is no digital secret for an attacker to extract, even if they compromise every cloud service in your stack.

Get your Burner
What to read next
Back to articlesPayment Psychology: Why Customers Spend More (And How Cash Businesses Can Use It)
Customers spend 64-177% more when the act of paying is separated from the act of buying. Disney, Starbucks, casinos, and cruise lines have all engineered their payment systems around that gap, while cash businesses sit at the opposite end, carrying the highest psychological friction of any payment method. This post breaks down the behavioral research behind the "pain of paying," explains why stored-value systems lower it, and shows how a Burner card loaded with stablecoins gives any small business access to the same spending psychology without building a proprietary platform.
The CLARITY Act Just Cleared the Senate. Here's What It Means If You Hold Stablecoins.
The Senate Banking Committee advanced the CLARITY Act on May 14, 2026, bringing the first comprehensive federal crypto market-structure bill closer to becoming law. The legislation splits oversight between the CFTC, SEC, and banking regulators while formally recognizing payment stablecoins under the GENIUS Act framework. Most notably for everyday users, Section 605 protects the right to self-custody through hardware and software wallets. This article breaks down what the bill actually changes for stablecoin holders, self-custody users, exchanges, and merchants accepting crypto payments.
What Are Stablecoins? A Plain-English Guide for 2026
Crypto can swing wildly in value, and that volatility is exactly what makes it impractical to use as everyday money. Stablecoins solve this by pegging a digital token to a stable asset, usually the US dollar, so it moves on blockchain rails without the price swings. This guide explains what stablecoins are, the five types and how each holds its peg, what they're actually used for, the main risks to watch for, and the simplest ways to buy your first one.